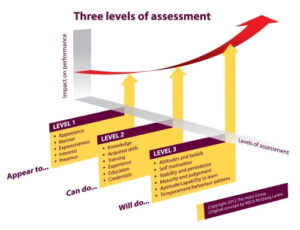
Corporate recruiters and staffing firms utilize various forms of screening interviews and candidate assessments but fail to measure role fit and team fit to help determine who makes the shortlist for for the Hiring Manager to consider. For executive recruiters it’s a combination of interview notes, references, details about accomplishments, and the recruiter’s gut feeling that these are the candidates to consider. Corporate recruiters and large staffing firms often add some type of DISC based behavioral test or aptitudes testing to help in their candidate assessments.
Candidate Assessments Fail on Team Fit
In the end the Hiring Manager thinks they are getting the best candidates available according to the recruiter’s gut feeling, the interview committee’s thoughts on a relatively short interview, and one or more candidate assessments (according to their HR, corporate recruiting/talent acquisition group, or external recruiter). But all too often failing to make sure the candidates being considered fit the role and are a team fit that will be a positive impact on team dynamics. What ends up happening is that a “C player”, a body that shows up and can perform the tasks but adds no real value, is hired.
Time after time I hear from VPs that within 6 months, a year or two AFTER a new hire that that “x” employee is okay, but he/she wishes the employee had the insight and ability to make better decisions, develop effective cost savings, or improve deliverables. This puts an added burden on the rest of the team that employee is working within, as well as the VP or manager who must figure out a way to make up for that employee’s lack of added value.
Team Dynamics are Improved with Proper Candidate Assessments
Hindsight shows that the candidate assessments are resulting in a shortlist delivered to the Hiring Manager prior to the face-to-face interviews and hire failed to address whether that candidate would be a “natural fit” for the team and what about that candidate would bring “real value” to making the overall team better. The most common, and mistakenly, the worst determining factor, is based primarily on whether the candidate has the skills, experience, and track record of past accomplishments to do the job.
This is a rote exercise where the recruiter matches up the responsibilities of the role with past work history and matches requirements with skills on a resume. The Hiring Manager and his/her interview team then “guess” if the candidate’s personality and communications style will tell them id he/she is a team fit. Yes that is a guess as those latter parts are determined by a few or a committee whose members spent at the most a few hours in a prefabricated interview process face-to-face with the candidate.
Tragically, these candidate assessments and screening processes result in recruiters delivering the “C player” and occasionally a “B player” or the company hiring someone who will reveal they lack in key interpersonal areas or were the wrong team fit. What the recruiter should have done is take the objectives, aka the end game of the role into consideration. Responsibilities on a job description rarely give more than a very brief sentence or two about the objectives.
The recruiter should get with the Hiring Manager to discuss the short-term and long-term objectives of the role apart from the responsibilities. The second factor is whether the potential candidate is a cultural and team fit. This is where the recruiter fails most often as companies are too eager to use a corporate public image profile of their culture they would either like the public, their employees, or customers to believe in or that they desire to attain.But the truth is EACH DEPARTMENT is unique.
 One needs to consider the team profile the candidate will be working within to then analyze if a candidate is a team fit. This means taking into consideration that team’s natural and adaptive communications styles, values and motivations, and decision making traits in order to identify a Team Profile.
One needs to consider the team profile the candidate will be working within to then analyze if a candidate is a team fit. This means taking into consideration that team’s natural and adaptive communications styles, values and motivations, and decision making traits in order to identify a Team Profile.
Since we are not all born and raised in the same place, geographical culture, education, religion, and family dynamics of individuals play a big part in this – especially in the relational side of how one views his/her self and views others.
Many vendors provide different forms of scientific, or skills-based, or psychometric, or behavioral testing and candidate assessments software. Most are one-size fits all in their approach and fail to take the skills, interview notes, and other aspects into consideration.
And without FIRST developing an ACCURATE Team Profile, you cannot know whether that candidate will be a “natural fit” as these tests and assessments are too one-sided. Sadly, this leads to often hiring the wrong person.
The third factor is the relevant accomplishments. Again this all too often is another rote exercise where recruiters miss the boat. Just because candidate “x” has this and that accomplishment for a direct competitor does NOT mean they will have similar success in a new role. You have to look at the team fit, company culture, team profile, and customer base dynamics he/she was working for in order to verify the accomplishments are really relevant to THIS new role.




 The business strategy of “sustainability” has been part of C-Level vocabulary for many years and it can mean different things to a CEO and his/her executive team depending on the business they are in. Manufacturing companies need to be mindful of environmental waste regulations.
The business strategy of “sustainability” has been part of C-Level vocabulary for many years and it can mean different things to a CEO and his/her executive team depending on the business they are in. Manufacturing companies need to be mindful of environmental waste regulations.
 Even on difficult searches – I’ve had several of “finding the needled in the haystack” where there were a very limited number of individuals who could meet/exceed the role objectives, it’s still the easier part of a search.
Even on difficult searches – I’ve had several of “finding the needled in the haystack” where there were a very limited number of individuals who could meet/exceed the role objectives, it’s still the easier part of a search.


 Mobile may not be part of your company’s business model right now, but it is coming. If you already have it, what are you doing to make things secure? What’s in your company’s written mobile device policy? How do you enforce it? How do you monitor the devices, especially if you are BYOD?
Mobile may not be part of your company’s business model right now, but it is coming. If you already have it, what are you doing to make things secure? What’s in your company’s written mobile device policy? How do you enforce it? How do you monitor the devices, especially if you are BYOD?