In regards to long range commercial drone control, according to wireless technology company Qualcomm, “5G connectivity will enable a worldwide boom in drone use, for fun, research, and business.” But for now, U.S. drone activity is limited to line-of-sight control. Regulations will need to catch up to the fast-developing technology.to enable the future of long range commercial drone control.
“A Highway in the Sky”
Research on the control of drones parallels work being done on autonomous vehicle technology. Dr. Harita Joshi of the University of Warwick spoke to Telecom TV about the development of ultra-reliable and low latency 5G networks that would allow for accurate communication with self-driving cars. Others are talking about “self-flying aircraft”.
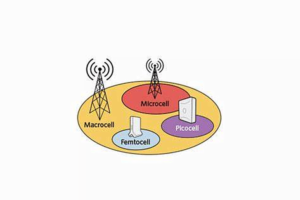
China Mobile used the term “flying automotive” when referring to the 5G drone network they were testing with Ericsson in 2016. Achieving end-to-end latency of 15 milliseconds, their 5G drone was able to make handovers between towers shared with normal cell phone users.Commercial long range drone control is in deep development. Take Alphabet (aka Google) who’s been working on ways to deliver mobile connectivity from the air. In 2014 they bought Titan Aerospace and turned it into Project Skybender.
The aim was to launch a fleet of lightweight, solar-powered drones that would fly in the upper atmosphere for up to 90 days at a time. Alphabet abandoned Skybender in 2016, preferring to concentrate on the use of balloons through their Project Loon. Another venture in long range drone control is Qualcomm, who want their unmanned aerial system (UAS) to be autonomous through development of UAS Traffic Management (UTM) controls. Director of Marketing Maged Zaki blogged about the “Path to 5G: Building a highway in the sky for autonomous drones”. “When UTM systems are deployed, we envision fleets of drones flying missions autonomously while connected to operators and regulators.”
Reaching Long Range Commercial Drone Control
No one wants to worry about drones falling from the sky. The FAA in the U.S. has restricted drone usage to Visual Line of Sight (VLOS). However, in 2016 the FAA granted an Extended Visual Line of Sight (EVLOS) operations waiver to commercial drone company Precision Hawk.
But for Beyond Visual Line of Sight (BVLOS) control of drones, operators need something more for long range commercial drone control. “Many of the anticipated benefits of drones, including delivery, inspections and search-and-rescue will require a highly secure and reliable connection,” said Qualcomm’s Chris Penrose, senior vice president, IoT Solutions, AT&T, according to a press release.

Dr. Joshi underscored in her interview the problem of latency and the need to service vehicles traveling at high speeds. The ITU published “IMT Vision”, a paper about 5G, in which they addressed these issues: IMT-2020 would be able to provide 1 ms over-the-air latency, capable of supporting services with very low latency requirements. IMT-2020 is also expected to enable high mobility up to 500 km/h with acceptable QoS.
To achieve the goals of long range commercial drone control, researchers are experimenting with a range of bandwidth called millimeter-wave radio. The new band spans from 30 to 300 gigahertz.
Way back in 1895 the polymath Jagadish Chandra Bose was experimenting in this spectrum. An August 2014 article in IEEE Spectrum tells the story: The intrepid scientist “sent a 60-GHz signal through three walls and the body of the region’s lieutenant governor to a funnel-shaped horn antenna and detector 23 meters away. As proof of its journey, the message triggered a simple contraption that rang a bell, fired a gun, and exploded a small mine.”
Despite the early research, attempts at harnessing millimeter-wave frequencies turned out to be extremely expensive and infeasible. The spectrum propagated poorly between towers and was scattered by rain. “The huge advantage of millimeter wave is access to new spectrum because the existing cellphone spectrum is overcrowded,” says Jacques Rudell of the University of Washington. The Guardian writer Mark Harris wrote about it when he broke the story “Project Skybender: Google’s secretive 5G internet drone tests revealed” in 2016. Despite Skybender’s demise, plans to harness millimeter-wave technology continue.
Bold Long Range Commercial Drone Control Projections
Hobbyists have taken to drones as a new tech toy, but other use cases will contribute to the drone boom. Companies like Alphabet hope to deliver internet to remote and under-served areas. Drones are useful in disaster recovery, search-and-rescue, and hazardous material situations. Amazon has already done long-range test deliveries. Pizza delivery by drone is not far away. And drone racing – like the 2016 World Drone Racing Championships in Hawaii – is a growing sport.
AT&T Foundry offered “10 Bold Projections on the Future of Drones”. These include swarming technology, onboard analytics, IoT support, AI and robotics, and the use of drones for dynamic communications networks. Whatever commercial applications await drone technology, it’s clear that they will be dependent on secure, fast, and reliable communications. 5G technology will likely play a significant role in the evolution of long range drone control.


 Same goes for accepting verbatim without question those provided by the candidate as they are so often former colleagues who are great friends unwilling to look past a biased lense. After identifying a target list of potential candidates through my Rolodex, networking, and referrals, I conduct one to two pre-screening interviews with the objective of understanding the motivations, skills/experience, and accomplishments of those potential candidates. If I am satisfied, they move forward to deeper interviews on my candidate shortlist.
Same goes for accepting verbatim without question those provided by the candidate as they are so often former colleagues who are great friends unwilling to look past a biased lense. After identifying a target list of potential candidates through my Rolodex, networking, and referrals, I conduct one to two pre-screening interviews with the objective of understanding the motivations, skills/experience, and accomplishments of those potential candidates. If I am satisfied, they move forward to deeper interviews on my candidate shortlist.
 Among list of recipients means that there are many personalities that is addressed to. Email marketing may tend to derail with what is the initial focus due to its mindset onto building lists and sending out numerous updates.
Among list of recipients means that there are many personalities that is addressed to. Email marketing may tend to derail with what is the initial focus due to its mindset onto building lists and sending out numerous updates.
 There are three types of job boards. First is the “major” such as Monster, CareerBuilder, The Ladders, etc. Second are the niche such as oilandgaspeople who claims to have 5,843 Active Recruiters 163,926 candidates or MedRepCareers which focuses on medical services, medical devices, and pharmaceutical sales jobs. Third are the job aggregators such as Indeed.com and SimplyHired.com. If you choose to use the former’ let this be a warning : job boards pitfalls and privacy issues means you will likely to receive loads of emails about jobs related to “insurance and financial sales or analysts”, car sales, and “temporary full time jobs” offered by RPOs (recruitment processing outsourcing firms) or IT engineering services companies.
There are three types of job boards. First is the “major” such as Monster, CareerBuilder, The Ladders, etc. Second are the niche such as oilandgaspeople who claims to have 5,843 Active Recruiters 163,926 candidates or MedRepCareers which focuses on medical services, medical devices, and pharmaceutical sales jobs. Third are the job aggregators such as Indeed.com and SimplyHired.com. If you choose to use the former’ let this be a warning : job boards pitfalls and privacy issues means you will likely to receive loads of emails about jobs related to “insurance and financial sales or analysts”, car sales, and “temporary full time jobs” offered by RPOs (recruitment processing outsourcing firms) or IT engineering services companies.
 In order to enable these functionalities we are recently witnessing the rise and proliferation of IoT applications that take advantage of Artificial Intelligence and Smart Objects. Smart objects are characterized by their ability to execute application logic in a semi-autonomous fashion that is decoupled from the centralized cloud.
In order to enable these functionalities we are recently witnessing the rise and proliferation of IoT applications that take advantage of Artificial Intelligence and Smart Objects. Smart objects are characterized by their ability to execute application logic in a semi-autonomous fashion that is decoupled from the centralized cloud.



 Jump forward several years, and now we have streaming video, movies and more coming in over wireless and data from cellular providers. For the airline industry, this is an absolute goldmine in IFEC profit margins.
Jump forward several years, and now we have streaming video, movies and more coming in over wireless and data from cellular providers. For the airline industry, this is an absolute goldmine in IFEC profit margins. 
 While HR policies work for most employees, the executive evaluation process is unique in that it measures the impact on the company’s essential point. Many companies make the fatal mistake of using a one-size-fits-all onboarding process driven by Human Resources which is really nothing more than an abridged orientation.
While HR policies work for most employees, the executive evaluation process is unique in that it measures the impact on the company’s essential point. Many companies make the fatal mistake of using a one-size-fits-all onboarding process driven by Human Resources which is really nothing more than an abridged orientation.
 Well, as it happened, this CEO was very impressed by the actual hand written letter and was a big believer in the snail mail personal touch. Funny thing is the HR Manager told me she thought it was “old school” and out of touch.
Well, as it happened, this CEO was very impressed by the actual hand written letter and was a big believer in the snail mail personal touch. Funny thing is the HR Manager told me she thought it was “old school” and out of touch.